info@waypro.hk
HONG KONG
DISTRIBUTED BRANDS












PRODUCTS
PLATFORM
VIRTUALIZATION
Create your own virtual farm based on VMware, Hyper-V, KVM, Xen or Citrix to reach maximum fexibility and utiliziation of your infrastructure
SERVERS
Build a new Server infrastructure on x86 or SAPRC architecture as well as upgrade your farm to meet current challenges
CLOUD SOLUTIONS
Next step of your IT-freedom. Choose Amazon Web Service or Microsoft Azure or other provider and forget about HW or SW support. Looking for PaaS / IaaS / SaaS?
PROJECT-BASED SERVICES
One of the software outsourcing modalities is the Project-Based Model services. It is a very useful mechanism to develop a project when you have a very clear and defined idea of what you want to create. You deliver your project plan to a technology partner and this team is responsible for developing it from start to finish
PRODUCTS
ENDPOINT PROTECTION PLATFORM (EPP)
EPP is the most common and effective malware prevention
approach and accepted as a basic security hygiene for all
organizations.
Mass spread threats (such as WannaCry and NotPetya) may cause
great damage to business operations and infrastructure.
A properly configured and maintained EPP product can
significantly reduce the attack surface, ransomware, and other threat risks.
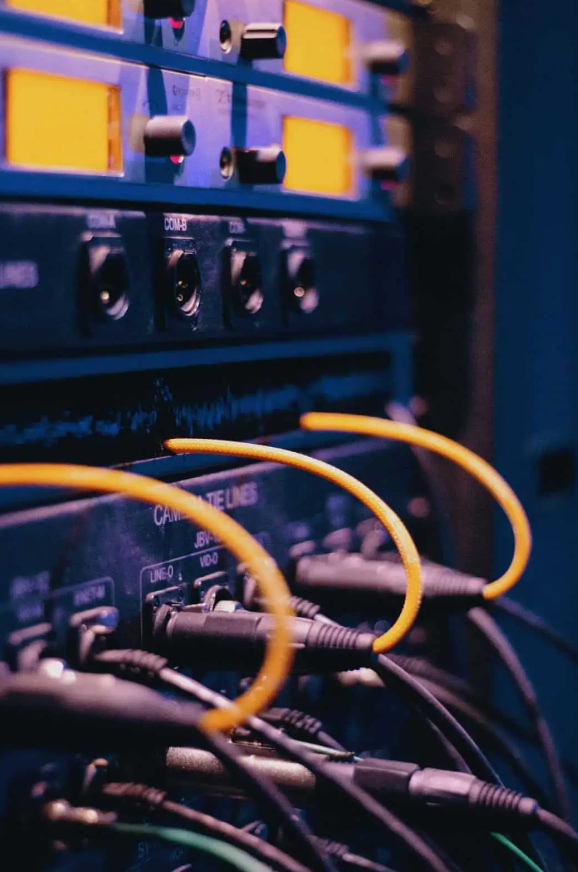
Network Security Solutions
In order to achieve a holistic network security approach,
it is necessary to use different and/or integrated solutions
in many areas for protection, detection, analysis and increasing network efficiency.
WAYPRO provides project design, installation, configuration
and maintenance services with its technical experts that has international certifications.
EPP Generations
3rd gen:
- A centrally managed EPP with audited and optimized settings
- Standard hardware, secure OS, and apps
- Minimum authorization management
- Removable media management
- Reduction of security abuses with reporting and central management for vulnerabilities and patches
- Using EDR with EPP, which uses modern inspection methods such as ML
- Using behavioral analysis which inspects and prevents malware
- Memory protection capabilities
- Automatic integration with Sandbox
- Using server-side HIPS, FIM, virtual patch management and micro-segmentation
- Application control and inspection
- Isolation of risky processes and prevention of affecting other processes by encapsulation
- Using deception technologies
- Advanced endpoint behavioral analysis, breach detection and intervention
- Endpoint forensic tools
ENDPOINT DETECTION AND RESPONSE
- Detects local events that can’t be seen through the network
- Provides detailed telemetry related to the attacker’s actions on each system
- Covers remote systems that are not on the company network
- Is not dependent on log activation
- Is not affected by network encryption technologies
- Can be applied to virtualized environments
NETWORK SANDBOX
Network Sandboxes are based on sensors on monitoring network traffic. They send suspicious objects (i.e. executable files, Microsoft Office files, PDF files and JavaScript codes) to a virtual domain environment where they will be automatically analyzed for detecting if they contain malware. Sensors may be private devices (or virtual devices) and can be placed in other security products (i.e. firewalls, secure web gateways and secure e-mail gateways can all function as sensors). Sandbox in a nutshell, produces a signature (vaccine) that makes detection easier for other security products, analysis, and detection of a harmful APT file by executing downloaded files on virtual machines.
The acceptance of cloud based virtual domain services enables easier integration of virtual domain as a feature of a main security product (i.e. firewall, secure web gateway and other products), for this reason it has a more common implementation. According to the regulations in GDPR, on-premise solutions are preferred to cloud solutions.
SIEM
Targeted attacks and broad base malicious software infections that cause breaches and data loss, makes the threat detection to buy SIEM technologies primary reason. Manufacturers are developing security analytics capabilities that range from basic features (including statistical fundamentals or trends which are part of basic product functionality) to advanced identification based on UEBA, machine learning that are provided by third parties or developed internally. SIEM technologies are adopting incident response capabilities (through naturally, acquisition or integrations) by adding functions that provide security orchestration, automation, and response (SOAR) capabilities.
- Can be used to monitor local and out-of-network events within
- Provides more secure user profile creation data compared to approaches intended for the network or the endpoint
The Sandbox evolution
- (1G Sandbox), are independent physical devices that are used to identify advanced threats.
- (2G Sandbox), integrates with other devices with wider security architecture to detect advanced threats in an organization.
- (3G Sandbox) contains robust AI capabilities that can analyze both static and behavior.
SYSTEM SOLUTIONS
Even though the technology changes,
the expectations and needs of IT professionals don’t change that much:
- High performance
- Advanced security
- Low cost of ownership
- High scalability
- Easy management
- Seamless integration
In order to provide the right solution to our customers, we carefully follow the technologies of our global software and hardware manufacturer partners, then we install the right solution and integrate it into the existing system for our customers depending on the results of their needs analysis.
- Server Solutions
- Data Storage and Data Management
- Data Backup / Recovery
- Data Archiving
SERVER SOLUTIONS
You can get more than your expectations by choosing the right servers for your applications, making the correct configurations and managing them effectively.
Beyond the performance and cost criteria:
- Lower power consumption
- Easier scalability
- More business continuity
- Less maintenance needs
- Easier manageability
With our technical staff of certified system engineers, we contribute to your efficiency by offering brand agnostic server solutions.
DATA STORAGE & DATA MANAGEMENT
We offer backup and recovery solutions to keep your ever-growing data accessible, usable and protected.
It is one of the critical tasks of system administrators to take data backups at regular intervals due to either legal obligations or internal policies of companies. Because of the constantly increasing amount of data, backing up times are getting longer and longer and sometimes there will be instances where data backups cannot be taken due to time constraints. In the risk of a data loss due to natural disasters, security vulnerabilities or user errors, our data backup and recovery infrastructure will be a life saver for you.
We offer solutions to our customers who want a new backup and recovery system or want to speed up their existing system. First, by analyzing the situation we:
Analyze the existing backup and recovery infrastructure,
Determine the backup and recovery method,
Determine the backup and recovery policy and plans
Design and set up backup and recovery infrastructure.
Within our backup and recovery solutions, we provide higher performance, lower bandwidth and storage costs thanks to our data deduplication, compression and replication technologies.